New for 2023:
Securing the Supply Chain: Maintaining Software and Data Integrity
Ensuring the integrity of software and its data is essential to support a secure software supply chain. This course focuses on mitigating supply chain attacks that violate software and data integrity, emphasizing security controls across the development, build, and deployment phases of the SDLC.
eLearning Platform
An Evergrowing Library We are constantly refreshing existing courses and developing new ones. There are over 30 courses in our catalog for developers, architects, managers, and leaders. The entire catalog is available for one price,. Single courses are available for purchase as well.
Built By Experts Decades of experience in application security and education ranging from training, threat modeling, code review, penetration testing, secure development lifecycle, as well as automation development.
Engaging Content Professional animators and professional voice actors help deliver a stunning experience, keeping viewers engaged and entertained while they absorb key application security concepts.
Flexible Deployments eLearning library of courses are authored in SCORM v1.2, SCORM v2004 3rd Edition, AICC, LTI 1.1, LTI 1.3 formats thereby enabling Cloud Hosted and Self Hosted deployment options.
Role-Based Training Depth of offering best suited for multi-year role-based training initiatives targeting developers, architects, testers, managers and more.

eLearning Program Strategy
Role-Based Applications Security Training Program
Business Team
Secure Manager
Secure Developer
Secure Architect
Secure Tester
Testimonials
“My team was unexpectedly hit with a PCI audit by a potential Client, and our Application Security Training program really helped us shine.”
“The development teams were extremely receptive to these training materials… not something we experienced in the past with our previous vendor.”
“I’m seeing a measurable improvement in the secure development skills of my team after integrating Infrared training in our process.”
Complete Application Security Course Catalog
APP SEC ESSENTIALS SERIES
| INTEGRATING SECURITY THROUGHOUT THE SDLC | 1 hour | |
| APP SEC FOUNDATIONS | 1 hour | |
| APP SEC FOUNDATIONAL EXAM | 30 minutes | |
| APP SEC FOUNDATIONS FOR MANAGERS | 1 hour | |
| SECURING THE SUPPLY CHAIN: MAINTAINING SOFTWARE AND DATA INTEGRITY AUDIENCE | 30 minutes | |
| MOBILE APP SEC FOUNDATIONS FOR MANAGERS | 1 hour | |
| APP SEC FOUNDATIONAL EXAM FOR MANAGERS | 1.5 hours | |
| APP SEC FOUNDATIONS FOR DEVELOPERS LEARNING PATH: | 4 hours | |
| INJECTION | 15 minutes | |
| BROKEN AUTHENTICATION | 30 minutes | |
| SENSITIVE DATA EXPOSURE | 25 minutes | |
| XML EXTERNAL ENTITIES | 15 minutes | |
| BROKEN ACCESS CONTROL | 30 minutes | |
| SECURITY MISCONFIGURATION | 25 minutes | |
| CROSS-SITE SCRIPTING | 25 minutes | |
| INSECURE DESERIALIZATION | 20 minutes | |
| USING COMPONENTS WITH KNOWN VULNERABILITIES | 15 minutes | |
| INSUFFICIENT LOGGING AND MONITORING | 20 minutes | |
| SERVER-SIDE REQUEST FORGERY | 15 minutes | |
| MOBILE APP SEC FOUNDATIONS FOR DEVELOPERS | 3 hours | |
| API SECURITY | 1.5 hours | |
| FOUNDATIONAL EXAM FOR DEVELOPERS | 1 hour |
Operations & Compliance
strategies covering industry-recognized taxonomies.
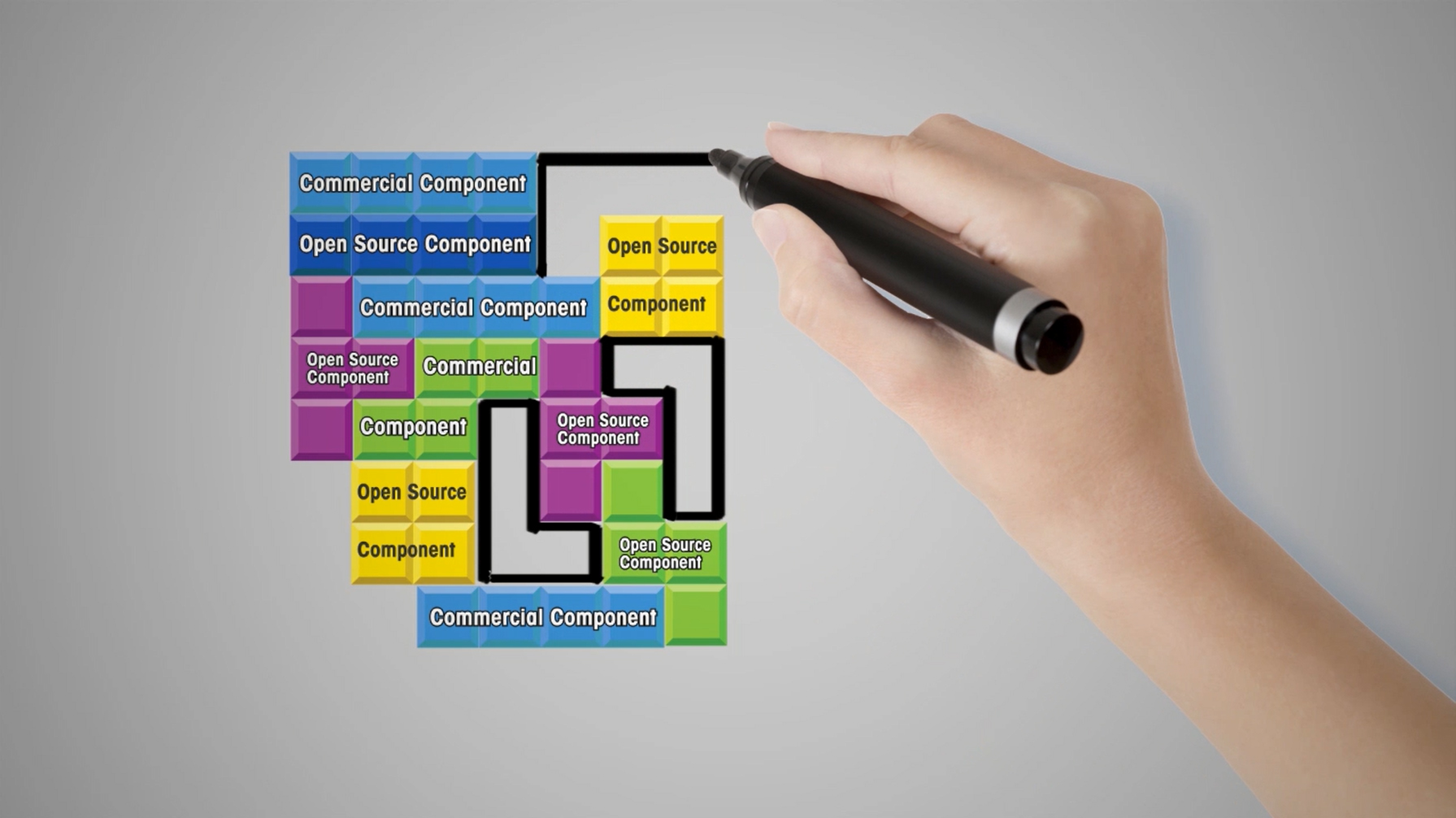
Building Secure Applications Series
variety of programming languages and technology stacks.
| BUILDING SECURE .NET APPLICATIONS | 1 hour | |
| BUILDING SECURE JAVA APPLICATIONS | 1 hour | |
| BUILDING SECURE JAVASCRIPT APPLICATIONS | 1 hour | |
| BUILDING SECURE C/C++ APPLICATIONS | 30 minutes | |
| BUILDING SECURE PYTHON APPLICATIONS | 1 hour | |
| BUILDING SECURE RUBY APPLICATIONS | 1 hour | |
| BUILDING SECURE MOBILE APPLICATIONS | 1 hour | |
| BUILDING SECURE GO APPLICATIONS | 1 hour |
Top 10 Topics
| A1 – INJECTION: Learn how to identify and secure the use of interpreters with a focus on SQL Injection. |
| A2 – BROKEN AUTHENTICATION AND SESSION MANAGEMENT: Learn about the most common attacks used against identity verification and management controls. |
| A3 – CROSS-SITE SCRIPTING (XSS): Learn about the most prevalent vulnerability facing developers today – Cross-Site Scripting. |
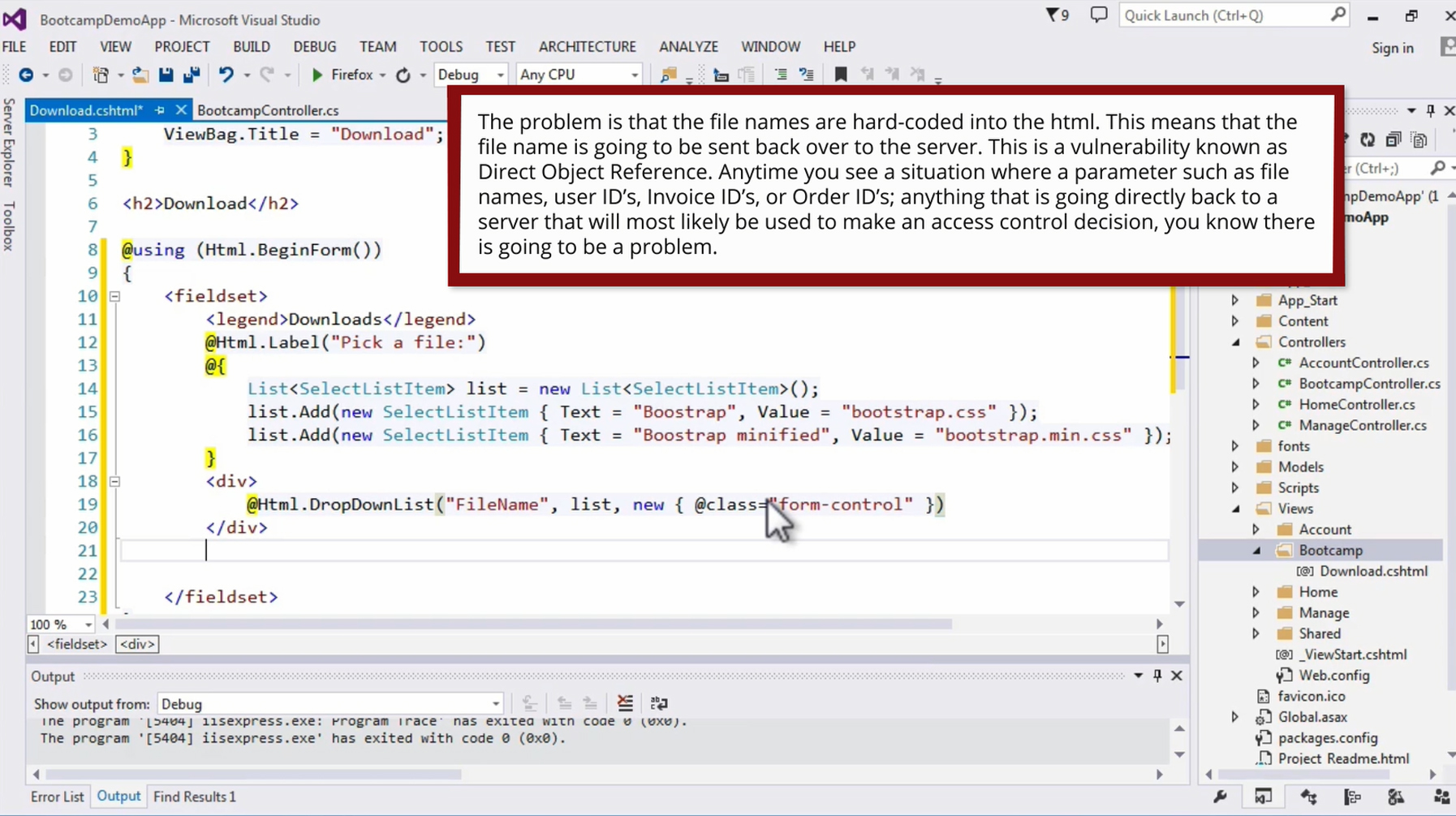
| A4 – INSECURE DIRECT OBJECT REFERENCES: Learn about the risks of exposing sensitive resource identifiers without proper authorization verification. |
| A5 – SECURITY MISCONFIGURATION: Learn about the core principles needed to properly secure environmental configuration files. |
| A6 – SENSITIVE DATA EXPOSURE: Learn about data classification and sensitive data management throughout the application layers. |
| A7 – MISSING FUNCTION LEVEL ACCESS CONTROL: Learn how to design, implement, and integration function level access control API. |
| Column 1 Value 10 |
| A8 – CROSS-SITE REQUEST FORGERY (CSRF): Learn how the synchronizer token pattern can thwart the sleeping giant that is Cross-Site Request Forgery. |
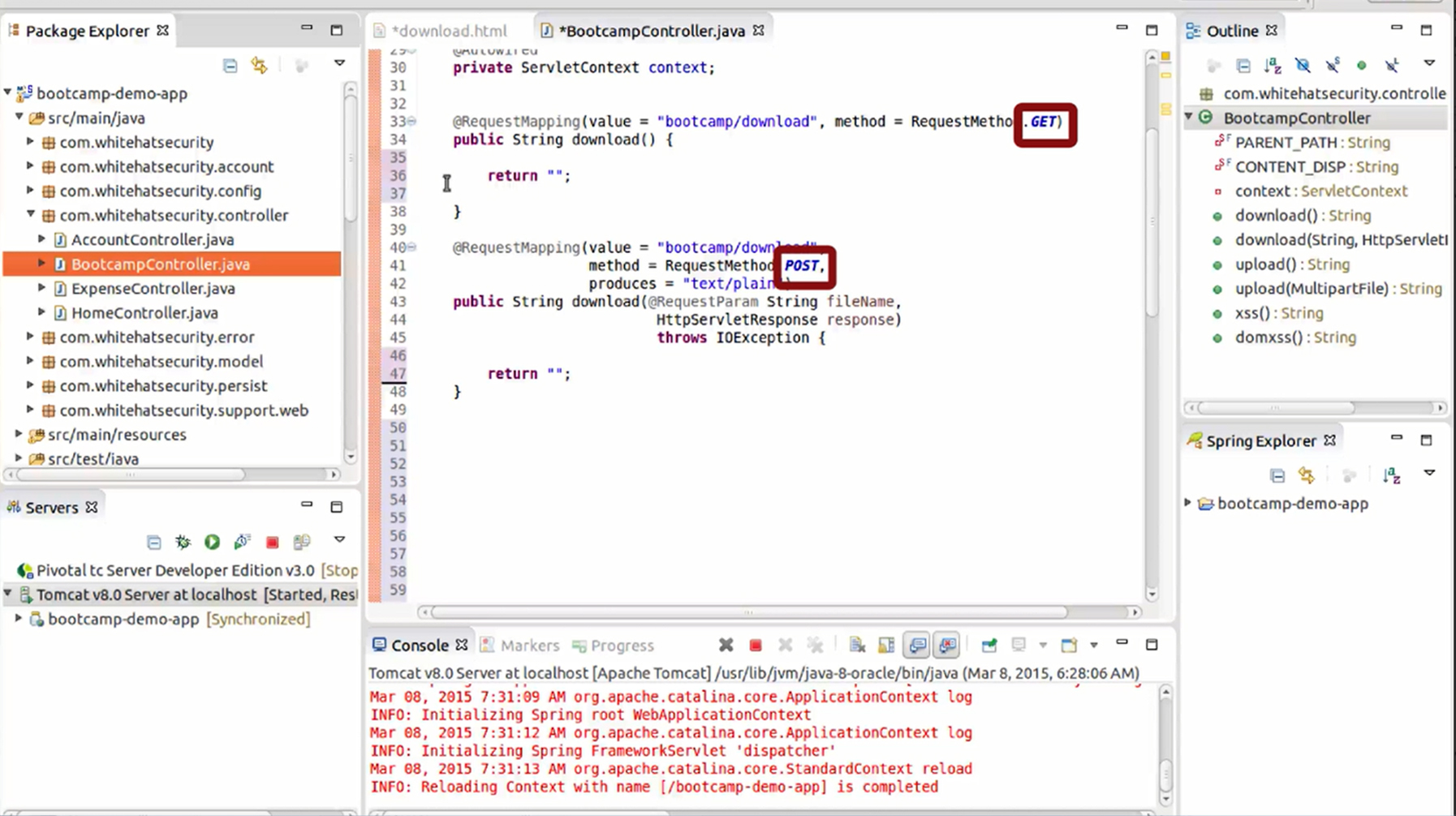
| A9 – USING COMPONENTS WITH KNOWN VULNERABILITIES: Learn about the need for visibility into the security of 3rd party components used by applications. |
| A10 – UNVALIDATED REDIRECTS AND FORWARDS: Learn how validation and indirection can be used to verify redirect and forward destinations. |